Getty Photos
Mac malware that steals passwords, cryptocurrency wallets, and different delicate knowledge has been noticed circulating by way of Google advertisements, making it at the very least the second time in as many months the extensively used advert platform has been abused to contaminate net surfers.
The most recent advertisements, discovered by safety agency Malwarebytes on Monday, promote Mac variations of Arc, an unconventional browser that grew to become usually accessible for the macOS platform last July. The itemizing guarantees customers a “calmer, extra private” expertise that features much less muddle and distractions, a advertising message that mimics the one communicated by The Browser Firm, the startup maker of Arc.
When verified isn’t verified
According to Malwarebytes, clicking on the advertisements redirected net surfers to arc-download[.]com, a very pretend Arc browser web page that appears almost similar to the real one.
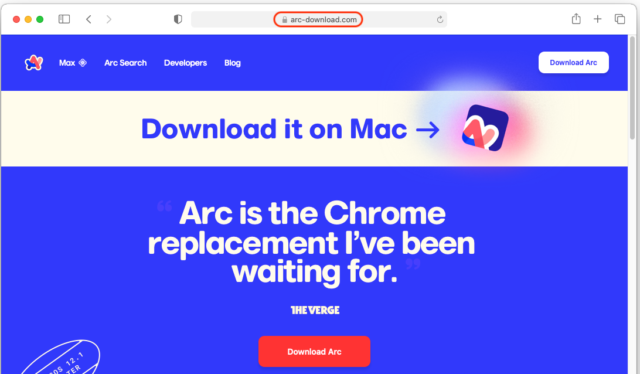
Malwarebytes
Digging additional into the advert reveals that it was bought by an entity known as Coles & Co, an advertiser id Google claims to have verified.
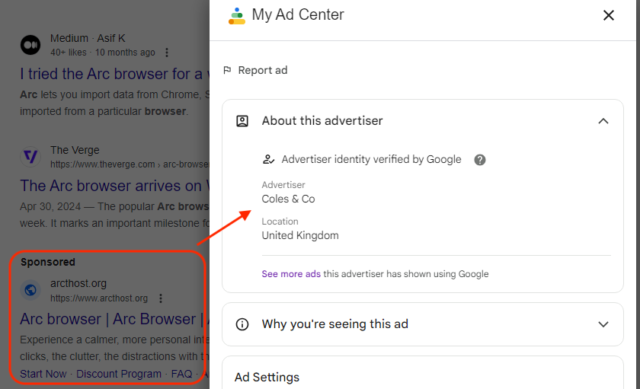
Malwarebytes
Guests who click on the obtain button on arc-download[.]com will obtain a .dmg set up file that appears just like the real one, with one exception: directions to run the file by right-clicking and selecting open, moderately than the extra simple methodology of merely double clicking on the file. The explanation for that is to bypass a macOS safety mechanism that forestalls apps from being put in until they’re digitally signed by a developer Apple has vetted.
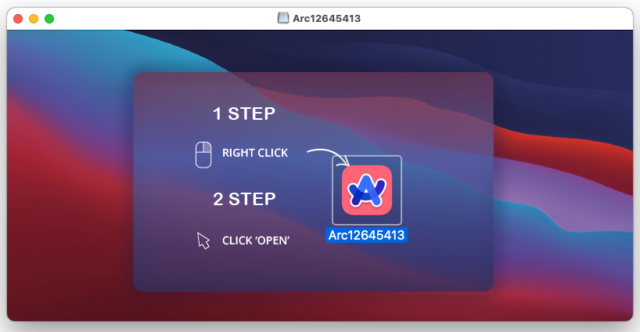
Malwarebytes
An evaluation of the malware code reveals that after put in, the stealer sends knowledge to the IP deal with 79.137.192[.]4. The deal with occurs to host the management panel for Poseidon, the identify of a stealer actively offered in legal markets. The panel permits prospects to entry accounts the place knowledge collected could be accessed.
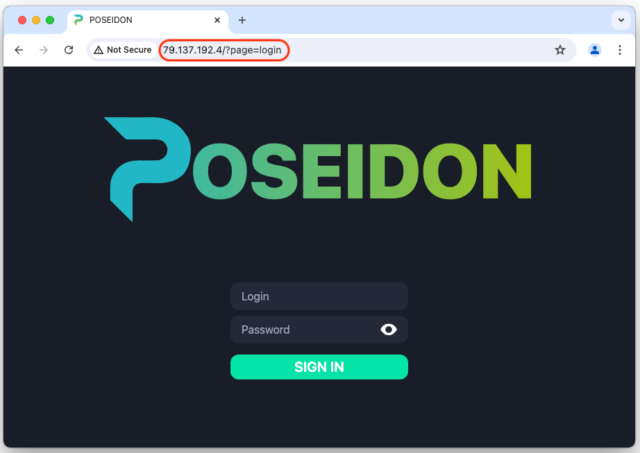
Malwarebytes
“There’s an energetic scene for Mac malware growth targeted on stealers,” Jérôme Segura, lead malware intelligence analyst at Malwarebytes, wrote. “As we will see on this submit, there are a lot of contributing components to such a legal enterprise. The seller must persuade potential prospects that their product is feature-rich and has low detection from antivirus software program.”
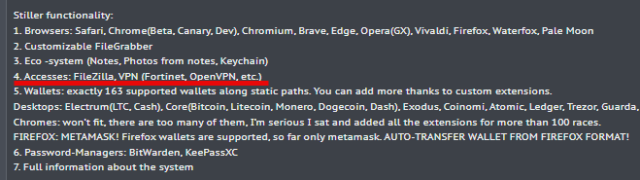
Poseidon advertises itself as a full-service macOS stealer with capabilities together with “file grabber, cryptocurrency pockets extractor, password stealer from managers akin to Bitwarden, KeePassXC, and browser knowledge collector.” Crime discussion board posts revealed by the stealer creator invoice it as a competitor to Atomic Stealer, an analogous stealer for macOS. Segura stated each apps share a lot of the identical underlying supply code.
The submit writer, Rodrigo4, has added a brand new function for looting VPN configurations, but it surely’s not presently purposeful, doubtless as a result of it’s nonetheless in growth. The discussion board submit appeared on Sunday, and Malwarebytes discovered the malicious advertisements at some point later. The invention comes a month after Malwarebytes identified a separate batch of Google advertisements pushing a pretend model of Arc for Home windows. The installer in that marketing campaign put in a suspected infostealer for that platform.
Malwarebytes
Like most different giant promoting networks, Google Adverts often serves malicious content material that isn’t taken down till third events have notified the corporate. Google Adverts takes no duty for any injury which will consequence from these oversights. The corporate stated in an electronic mail it removes malicious advertisements as soon as it learns of them and suspends the advertiser and has carried out so on this case.
Individuals who wish to set up software program marketed on-line ought to hunt down the official obtain web site moderately than counting on the positioning linked within the advert. They need to even be cautious of any directions that direct Mac customers to put in apps by way of the right-click methodology talked about earlier. The Malwarebytes submit offers indicators of compromise individuals can use to find out in the event that they’ve been focused.
